Introduction to Zero Trust Architecture Ecommerce Security
As online retail platforms grow more complex, attackers target identity and data flows across applications, third party services and payment systems. Zero trust architecture ecommerce security provides a disciplined approach that assumes no component is trustworthy by default and requires verification at every layer. This blog explains what zero trust means for ecommerce teams, outlines practical components, and offers a pragmatic path for implementing controls that protect customers, partners and revenue. For decision makers, the key takeaway is that security is an ongoing process tied to people, processes and technology, not a one time configuration. By adopting a risk based, identity driven model, modern ecommerce businesses can reduce blast radius and improve resilience across cloud and on premise environments.
What zero trust architecture ecommerce security means for online retail
Zero trust architecture ecommerce security is a philosophy as well as a technical framework. It starts from the principle that trust should never be assumed, regardless of where a request originates. In practice this means authenticating users and devices for each action, enforcing least privilege access, and continuously validating risk as data moves through the stack. For an ecommerce platform, this involves protecting the customer account, the payment gateway, order management systems, inventory feeds, and partner integrations. A practical model uses identity based access controls, devices with posture checks, and granular permissions that restrict each service to the minimum actions required. Microservices and API driven architectures demand explicit trust decisions at every interface, with service mesh or API gateways enforcing policies. By grouping assets into small, verifiable zones, you can limit the spread of breaches and maintain stronger control over sensitive data such as payment details and personal customer information. This section lays the groundwork for why zero trust is essential in ecommerce security and highlights the concrete steps needed to begin the journey.
Key components of zero trust architecture ecommerce security for ecommerce platforms
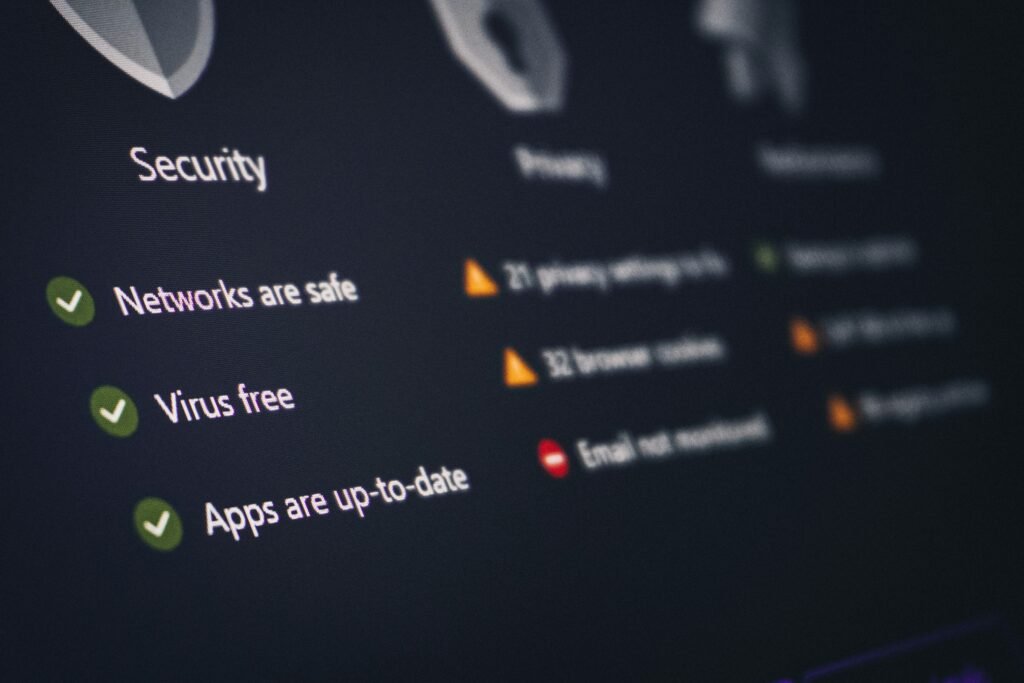
Implementing zero trust architecture ecommerce security relies on a set of interlocking components that work together to verify identity, protect data, and monitor activity. Identity and access management forms the backbone: strong authentication, multi factor options, and conditional access policies that respond to device health, location, and user risk. Single sign on simplifies user experience while maintaining security controls. Device posture checks and endpoint security determine whether a device is trusted enough to access sensitive applications or data. Encryption is essential for data in transit and at rest, with robust key management and secrets vaults for API credentials and service accounts. API security, rate limiting, and mutual TLS protect service communication. Finally, continuous monitoring, analytics and a well defined incident response plan ensure that anomalous activity can be detected and contained quickly. All of these components should be deployed with a clear governance model and regular review to keep pace with evolving threats and regulatory expectations.
Implementing zero trust architecture ecommerce security in ecommerce workflows
Implementing zero trust architecture ecommerce security requires a structured, incremental approach. Start with mapping data flows to identify where sensitive information travels and where access controls are critical. Identify high value assets such as payment processing, customer data stores, order information, and supplier portals, then create micro perimeters around these assets. Implement least privilege access for every service and role, and replace broad admin rights with just in time or just enough access. Deploy ZTNA for remote staff and contractors, and integrate with your existing IAM provider for consistent authentication. Enforce device posture checks before granting access to critical services, and implement continuous authentication strategies that re evaluate risk at key touchpoints. In parallel, adopt secure software practices across development and deployment pipelines, including code signing, software bill of materials and regular vulnerability management. This phased roll out helps manage cost, reduces disruption, and delivers measurable security improvements without compromising user experience.
Risks, challenges and practical mitigations
Adopting zero trust is not a single purchase or a one off configuration. It introduces complexity and ongoing governance. Common challenges include integration with legacy systems, managing policy complexity across multiple cloud environments, and balancing security with performance for a high velocity ecommerce site. To mitigate these risks, start with a prioritised plan that targets high impact areas such as payment processing or customer authentication. Use a phased rollout with measurable milestones, and ensure security teams collaborate closely with product, platform operations and PCI compliance teams. Align zero trust controls with data protection regulations such as GDPR and PCI DSS to avoid compliance gaps. Maintain clear incident response playbooks and ensure logging and telemetry are centralised so you can detect anomalies and respond quickly. A well documented roadmap helps stakeholders understand the value and keep momentum.
Measuring success with zero trust architecture ecommerce security
To demonstrate value, establish concrete metrics that reflect risk reduction, operational impact and business outcomes. Key performance indicators include time to verify and grant access, mean time to detect anomalous activity, and the proportion of privileged actions reviewed rather than automated. Track the number of access requests rejected or rerouted due to risk signals, and monitor the rate of policy exceptions. Regularly audit data access histories to verify that data minimisation and least privilege principles are upheld. Governance should include periodic penetration testing, red team exercises where appropriate, and routine review of supplier and partner access. By tying technical controls to business objectives, you can show how zero trust architecture ecommerce security protects revenue, reduces fraud exposure and strengthens customer trust.
Frequently Asked Questions
What is zero trust architecture and why is it important for ecommerce security?
Zero trust architecture is a security model that requires verification for every access request, regardless of where it originates. For ecommerce, this means protecting customer data, payment information and back end systems by enforcing strict authentication, device posture checks, least privilege access and continuous risk assessment. It reduces the chance that compromised credentials can lead to large breaches and enables safer collaboration with partners and cloud services.
How does zero trust affect PCI DSS and data protection for ecommerce?
Zero trust supports PCI DSS requirements by strengthening access controls, monitoring and data protection. It helps ensure that only authenticated and authorised entities can access payment data and sensitive systems, while encryption and robust key management protect data in transit and at rest. Ongoing monitoring and incident response capabilities align with the need to detect and respond to security events promptly, improving overall compliance posture.
What are practical first steps to start implementing zero trust in an ecommerce environment?
Begin with a data flow map to identify critical assets and sensitive information. Establish a phased plan focusing on high impact areas such as payment processing and customer data stores. Implement strong authentication, device posture checks, and least privilege access for key services. Introduce micro perimeters around critical assets and deploy ZTNA for remote users. Ensure governance and logging are in place, and set up regular reviews and testing to measure progress and adjust policies as needed.
Conclusion: Zero Trust Architecture Ecommerce Security for a resilient ecommerce
Zero trust architecture ecommerce security offers a principled path to protect modern ecommerce environments. By treating every access request as potentially risky and enforcing verification, businesses can reduce attack surfaces, protect sensitive data and sustain customer trust. The approach is most effective when implemented in stages, aligned with data flows and business priorities, and supported by strong governance, testing and continuous improvement. For decision makers, the payoff is clear: improved security posture without sacrificing performance or user experience. Embracing zero trust is not merely a technology choice; it is a strategic investment in long term ecommerce resilience.
Get expert help to plan your zero trust rollout
Contact TechOven Solutions to map your data flows, define high impact targets and design a phased zero trust rollout for your ecommerce platform.