Introduction to self-healing websites
For business owners, CTOs and decision makers, self-healing websites offer a pragmatic path to resilience. The concept combines continuous monitoring, automated remediation and robust deployment practices to keep services responsive when faults occur. At the heart are maintenance agents that watch performance, apply corrective actions and, when necessary, trigger safe fallbacks without awaiting human intervention. This approach does not replace skilled engineering; it augments capability, enabling teams to focus on higher value work while critical systems stay available. In this article we outline what self-healing websites are, how automated maintenance agents fit into the architecture, and how organisations can implement them responsibly. We cover governance, security considerations and the practical steps required to move from idea to operation. For decision makers, the objective is clear: increase reliability without sacrificing control or visibility over your digital estate.
What are self-healing websites?
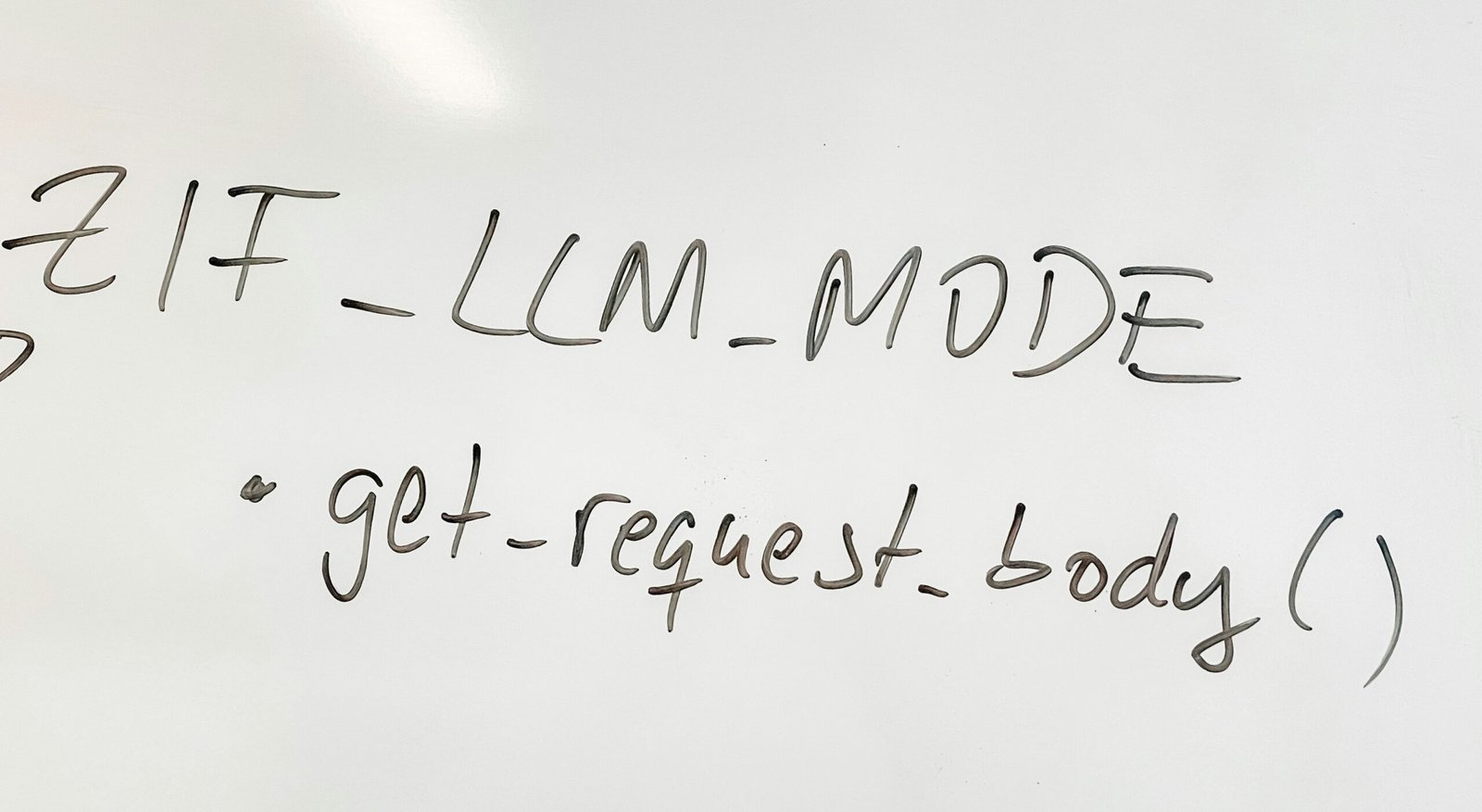
Self-healing websites are systems designed to recover from faults with minimal human intervention. They combine monitoring, automated remediation and resilient deployment practices to keep services responsive when errors occur. At the core are maintenance agents that watch for latency spikes, error rates, configuration drift and dependency failures. When a fault is detected, agents can execute predefined remediation steps such as restarting a service, clearing caches, reconfiguring routes or triggering a safe fallback. Importantly, self-healing does not assume perfection; it assumes imperfect systems and aims to minimise the duration of faults by applying repeatable, tested responses. In many organisations this approach starts with observable signals, a policy library that defines acceptable states, and an automation layer that translates signals into actions. The outcome is a more predictable runtime environment, with faster recovery times and richer telemetry for engineers.
Automation and maintenance agents: core components
Self-healing websites rely on a small set of well defined components working in concert. The first is a robust monitoring layer that collects metrics from every tier of the stack, from front end performance to back end services and databases. The second is a policy engine that encodes rules for when and how to act. This is typically device and service specific, but it should be auditable and version controlled. Third, remediation agents perform the actions, such as restarting processes, scaling services, or routing traffic to healthy instances. A fourth component is a knowledge base that captures proven responses and post incident reviews, ensuring actions improve over time. Finally, an orchestration layer coordinates these elements, handles dependencies and provides safe fallbacks and manual overrides for governance. Together, these components enable rapid, repeatable responses to faults while maintaining visibility for operators and stakeholders.
Designing effective self-healing workflows
Designing workflows requires balancing speed with safety. Start by mapping critical user journeys and identifying points where failures would have the greatest impact. Establish monitoring signals for each point and define clear, testable remediation paths. A typical workflow includes detection, decision making, action, verification and escalation if needed. Decision making should use policy checks, such as circuit breakers and idempotent actions, to avoid cascading failures. Remediation should be automated where safe, but with safeguards such as rate limits, timeouts and automated rollbacks. Verification steps validate that actions produced the desired outcome, using health checks or synthetic transactions. If the system cannot recover within a defined window, escalation routes should notify on call teams and provide actionable context. Finally, every workflow should be documented and version controlled, with periodic drills to test performance under stress. The goal is to create self-healing behaviour that is predictable, observable and auditable by design.
Benefits, risks and governance
Organisations implementing self-healing websites report improvements in resilience and incident response. The benefits include shorter incident durations, faster recovery and more consistent user experiences during outages. Because remediation is automated, human operators can focus on root cause analysis and system design rather than repetitive tasks. However there are risks to manage: automation must be built on reliable data, and misconfigured policies can cause unintended changes. Strong governance is essential, including access controls, change management, audit trails and regular reviews of automation rules. Security concerns also arise when automation can modify network routes, scale services or adjust credentials. It is important to embed security testing into the development cycle and maintain strict separation of duties. Compliance with data protection and regulatory requirements should be part of policy language. Finally, organisations should plan for ongoing maintenance of the automation framework itself, ensuring updates are tested and documented, and that any third party components meet your security and privacy standards.
Implementation roadmap for organisations
Turning a concept into operation requires a structured roadmap. Begin with a discovery phase to locate critical systems, determine the data needed for decision making and identify potential failure modes. Next, run a pilot on a representative subset of services to validate the governance model and measure impact on uptime and developer workflow. Use infrastructure as code and containerisation to make workflows repeatable and portable. Build a minimum viable automation layer that covers essential remediation actions and a clear rollback policy. As part of scale up, integrate the maintenance agents with your existing observability and incident management tools. Establish training, runbooks and on call rotation, ensuring teams understand how automated actions interact with human response. Finally, implement a governance framework that documents ownership, policy updates and audit procedures. The result is a scalable, auditable approach to self healing that respects organisational controls while delivering tangible reliability improvements.
Frequently Asked Questions
What is a self-healing website?
A self-healing website is a system that automatically detects faults and executes predefined remediation steps to restore normal operation with minimal human intervention. It relies on monitoring, policy driven decisions and automated actions to manage faults quickly. The goal is to reduce disruption and maintain a stable user experience while keeping human operators informed. Implementation typically starts with high priority services, clear recovery objectives and a structured playbook of responses that can be tested and audited.
How much does it cost to implement automated maintenance agents?
Costs vary depending on the scope, the existing tooling and the level of automation desired. A pilot project focusing on a small, critical service can be relatively affordable and demonstrates value before broader rollout. Ongoing costs include maintenance of the automation framework, updates to policy rules and coordination with monitoring and incident management tools. A well planned programme integrates with your DevOps practices, so savings come from faster recovery, fewer manual interventions and improved service reliability.
What are the security considerations for self-healing websites?
Key security considerations include strict access controls for automation runbooks, detailed audit trails of actions taken by agents, and secure handling of credentials and secrets. Policies should be reviewed regularly, and automation changes should go through established change control processes. It is important to isolate automated actions to prevent unintended access to sensitive systems, and to test automation under simulated attack scenarios. Regular security testing, dependency management and adherence to data protection requirements are essential components of a safe self-healing programme.
Conclusion
Self-healing websites powered by automated maintenance agents offer a practical path to greater operational resilience. By combining continuous monitoring, clear policy based actions and well governed automation, organisations can shorten fault durations and preserve a reliable user experience. The key to success lies in robust governance, careful risk management and ongoing refinement of remediation workflows. When implemented thoughtfully, self healing becomes a disciplined capability rather than a risky adjustment. For modern web estates, it represents a structured, auditable approach to maintaining performance in the face of evolving challenges.
Call to action
Contact TechOven Solutions to assess a self-healing strategy for your platforms.